The UK compliance automation platform from an IASME-licensed Cyber Essentials body.
65+ frameworks, 300+ integrations, real-time monitoring. Pair the platform with our IASME-licensed Cyber Essentials and you get a single UK vendor covering certification and ongoing compliance oversight.
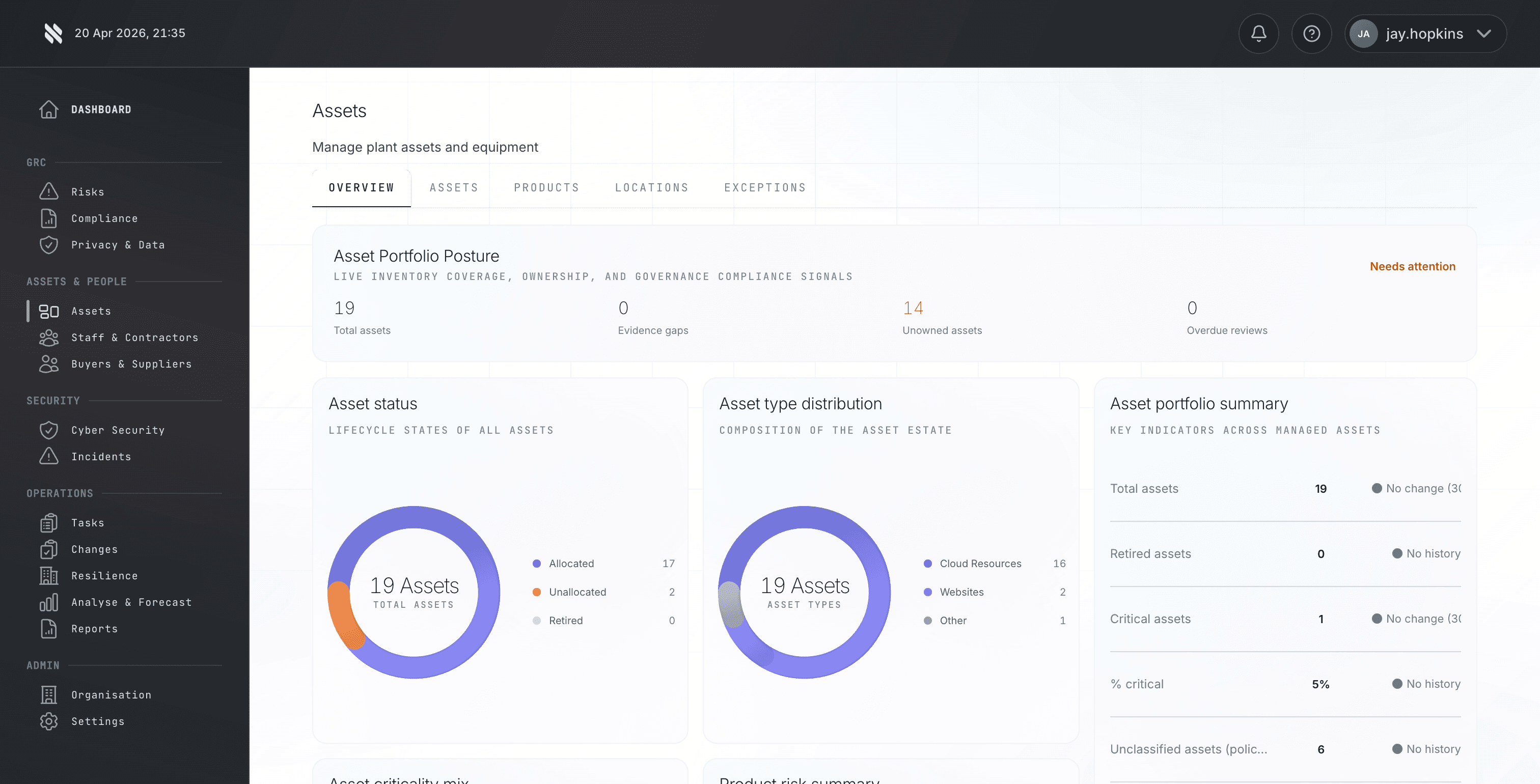
Discover / Asset Discovery
Know what you own before you decide what is at risk.
Build a live, governed asset register across hardware, software, cloud and service dependencies, with ownership and evidence attached from day one.
- Discover assets from connected tooling.
- Assign accountable owners and lifecycle status.
- Keep audit scope backed by live data.
Discover / Data Discovery
Find sensitive data, classify it, and govern where it moves.
Identify where critical and regulated data lives, who owns it, and which controls or privacy obligations apply.
- Classify data by sensitivity and business use.
- Connect data stores to suppliers and systems.
- Evidence privacy and compliance obligations.
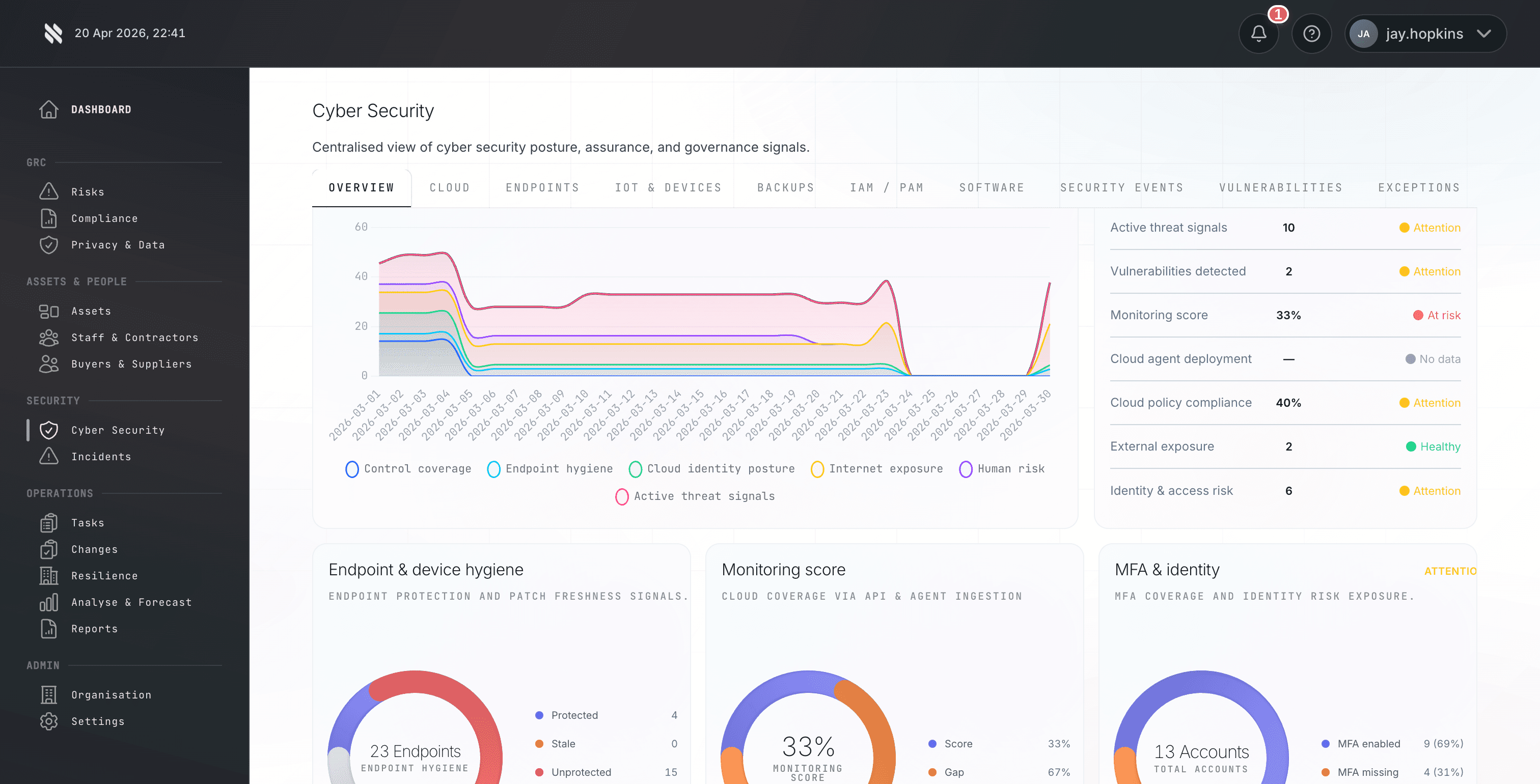
Protect / Vulnerability Scanning
Prioritise exploitable risk, not just high CVSS numbers.
Consolidate scanner output, enrich it with exploit context and asset importance, then drive remediation through accountable workflows.
- Normalise findings across scanners.
- Prioritise with exploit and asset context.
- Track remediation through to evidence.
Protect / Supply Chain Risk
See supply chain risk as part of your operating model.
Monitor suppliers, dependencies, control evidence and remediation actions without relying on annual questionnaires alone.
- Map suppliers to services and data.
- Track assurance evidence and actions.
- Surface third-party risk before renewal or procurement decisions.
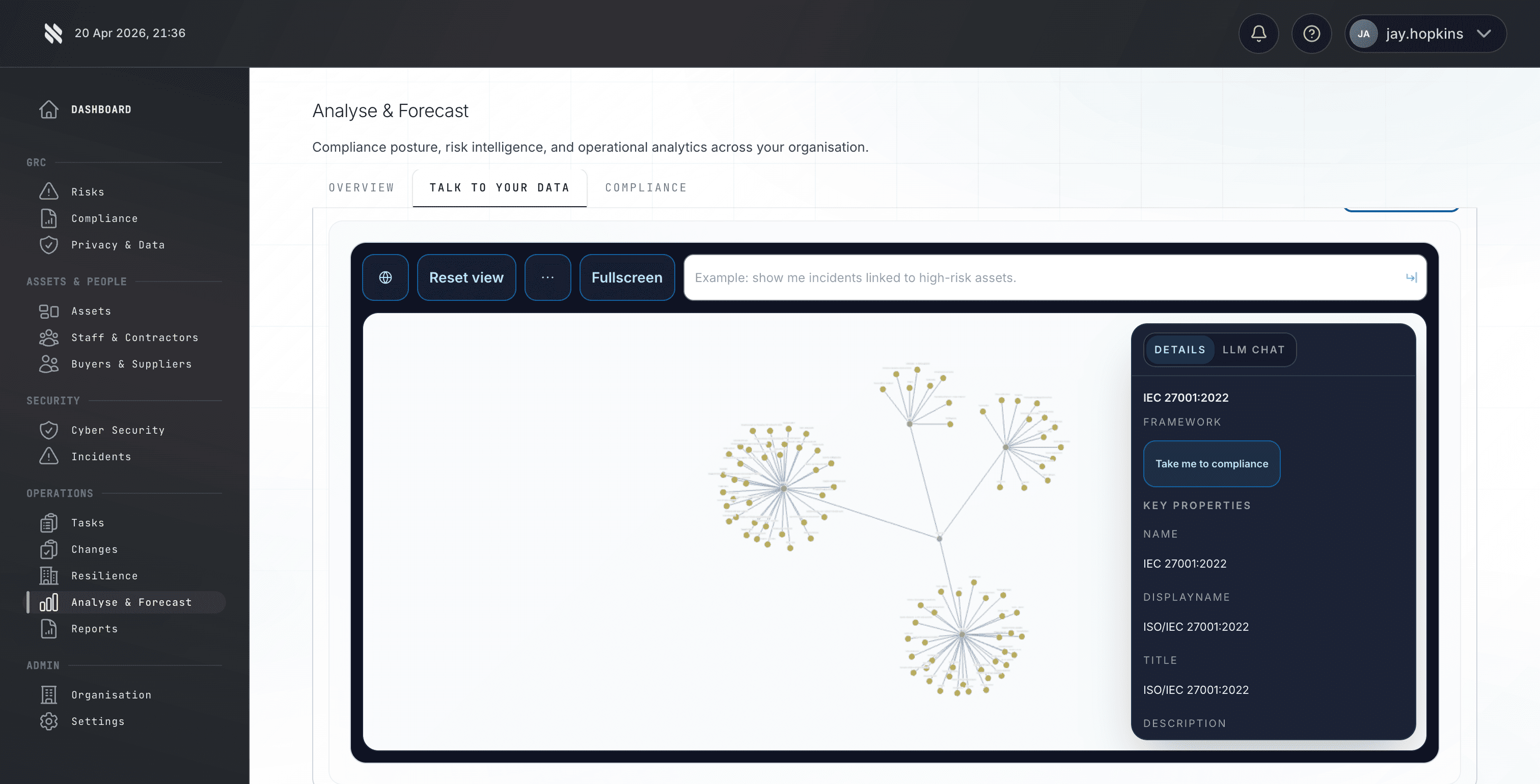
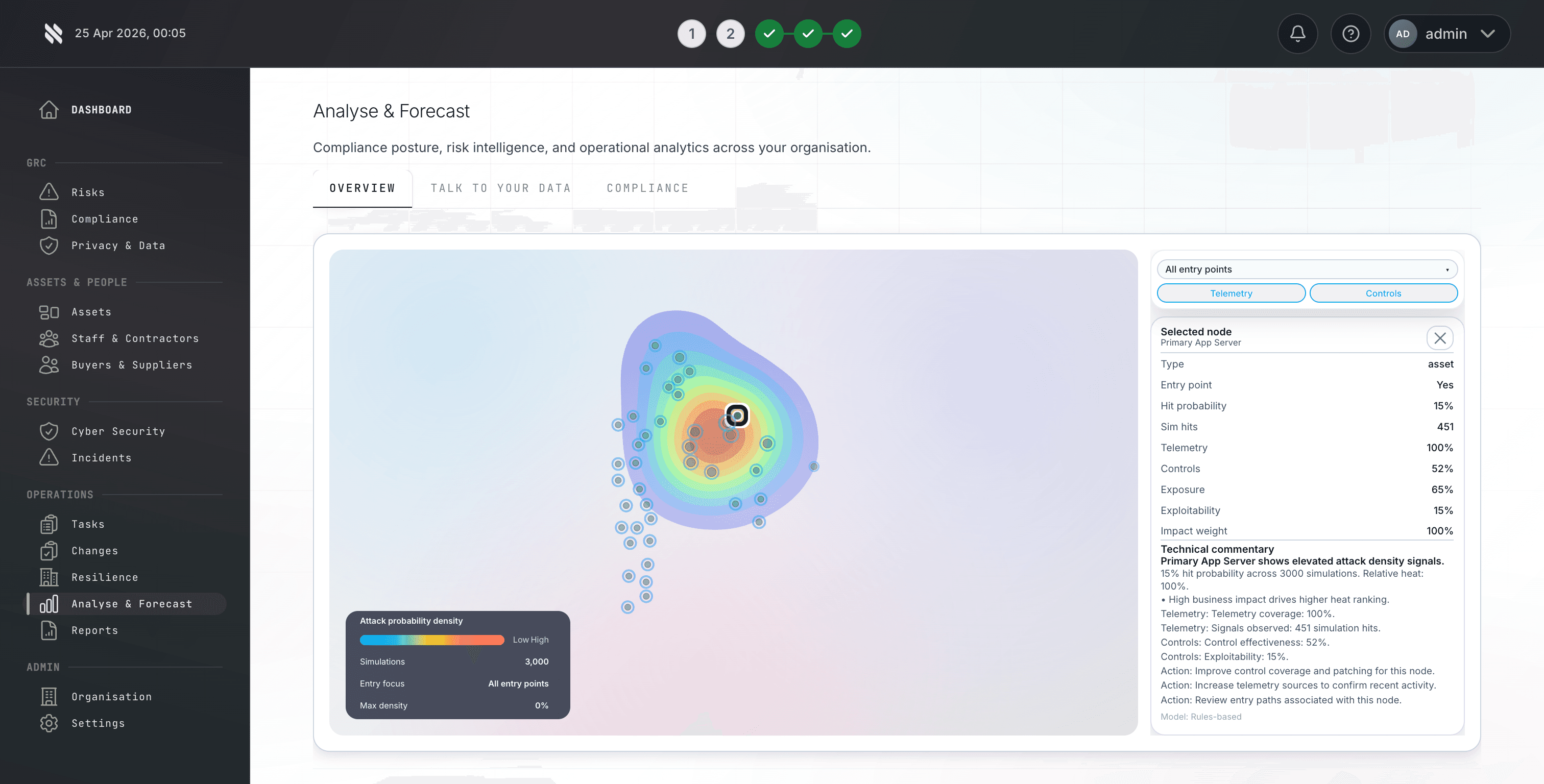
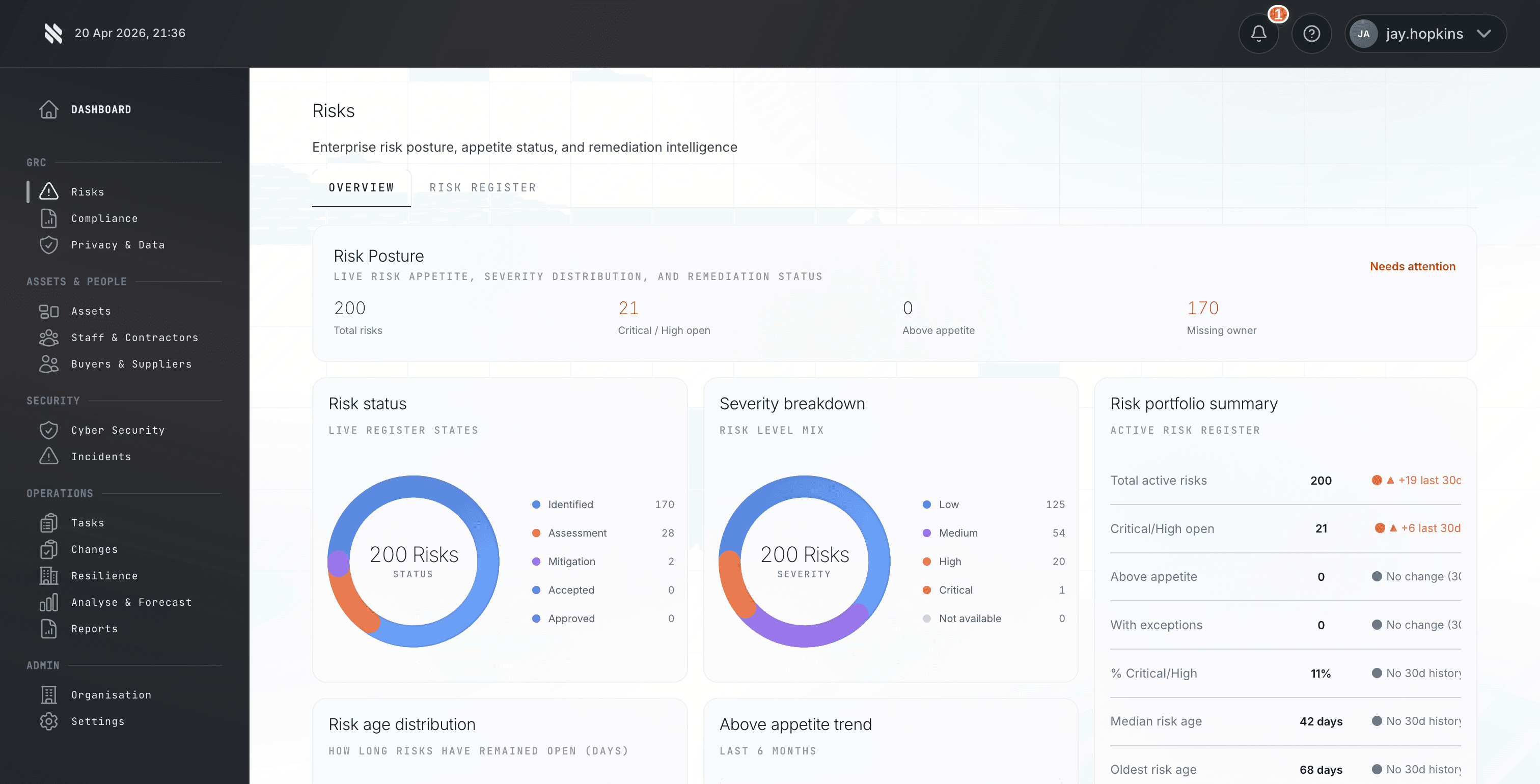
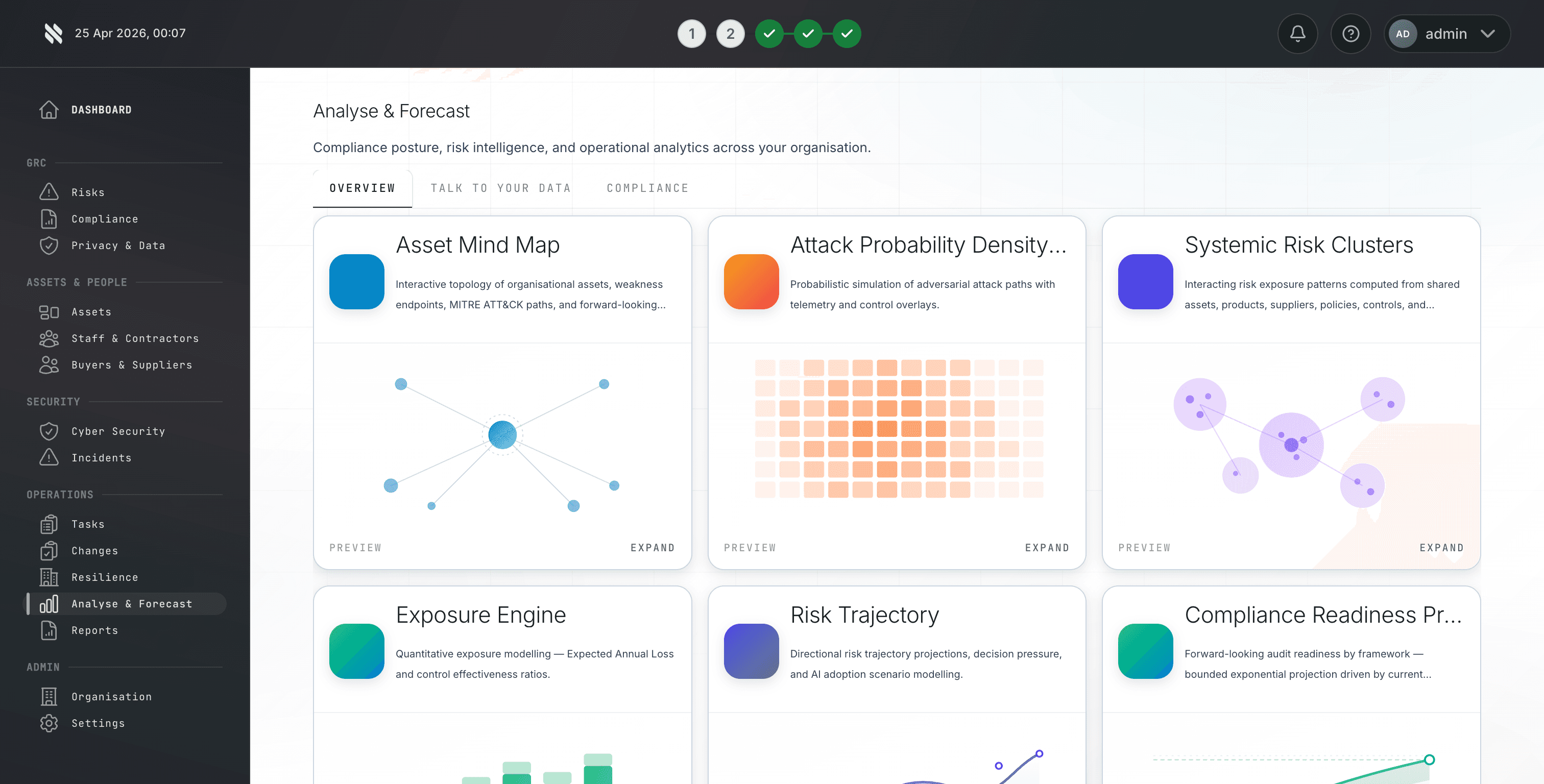
Protect / Exposure Modelling
Understand how small weaknesses combine into business risk.
Model how assets, vulnerabilities, suppliers and control gaps interact so teams can act on likely impact, not isolated findings.
- Link technical exposure to business services.
- Forecast risk concentration.
- Support better risk and insurance conversations.
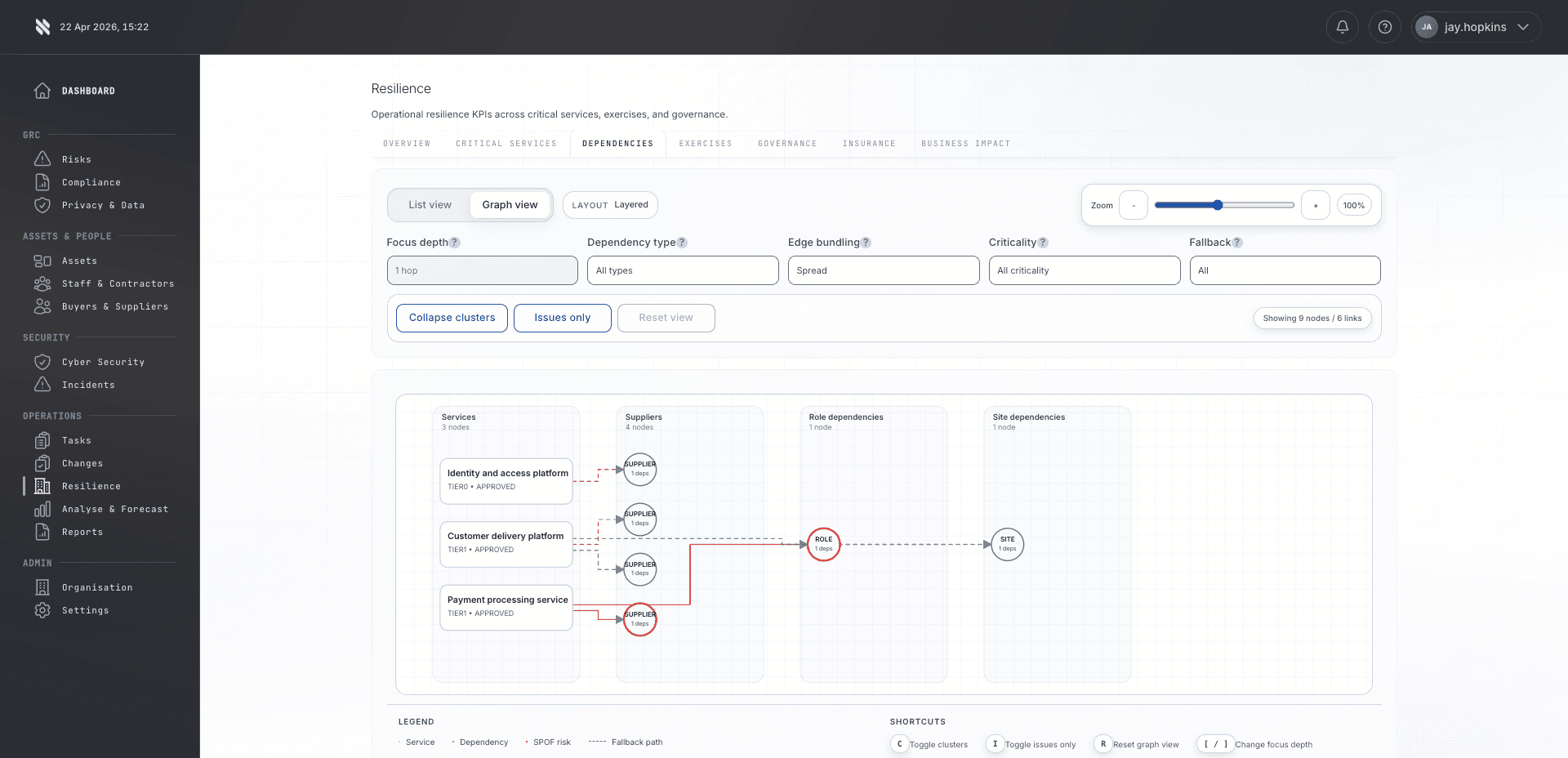
Protect / Continuity
Make resilience measurable, not theoretical.
Connect recovery plans, critical services, dependencies and test evidence so continuity planning reflects the real operating environment.
- Map services to assets and suppliers.
- Track tests and lessons learned.
- Evidence recovery readiness over time.
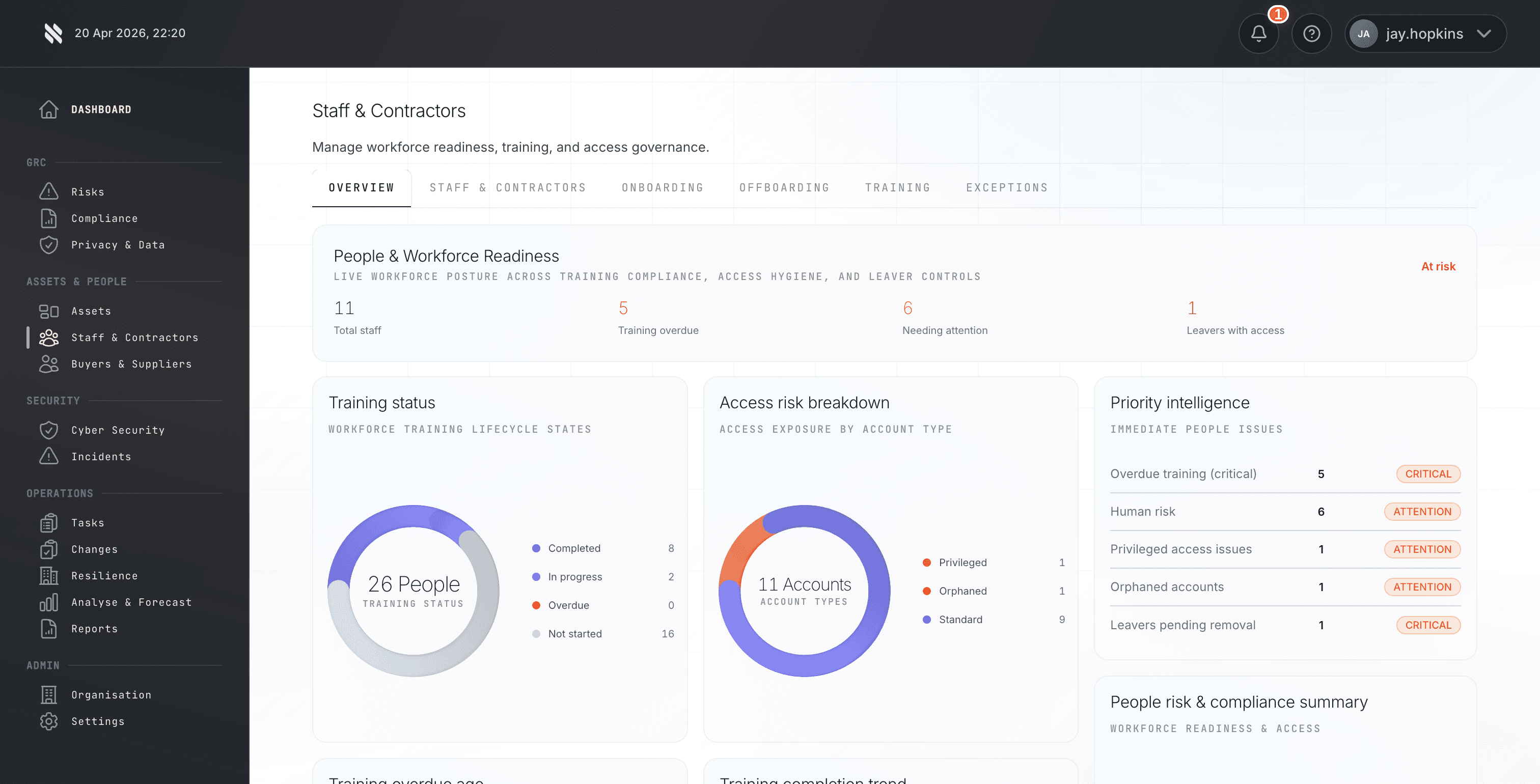
Protect / People Lifecycle
Govern people, access and accountability from joiner to leaver.
Manage onboarding, role changes, training, attestations and leaver controls as part of the wider security evidence model.
- Track people-related control obligations.
- Connect access and training to evidence.
- Expose gaps before assessment or audit.
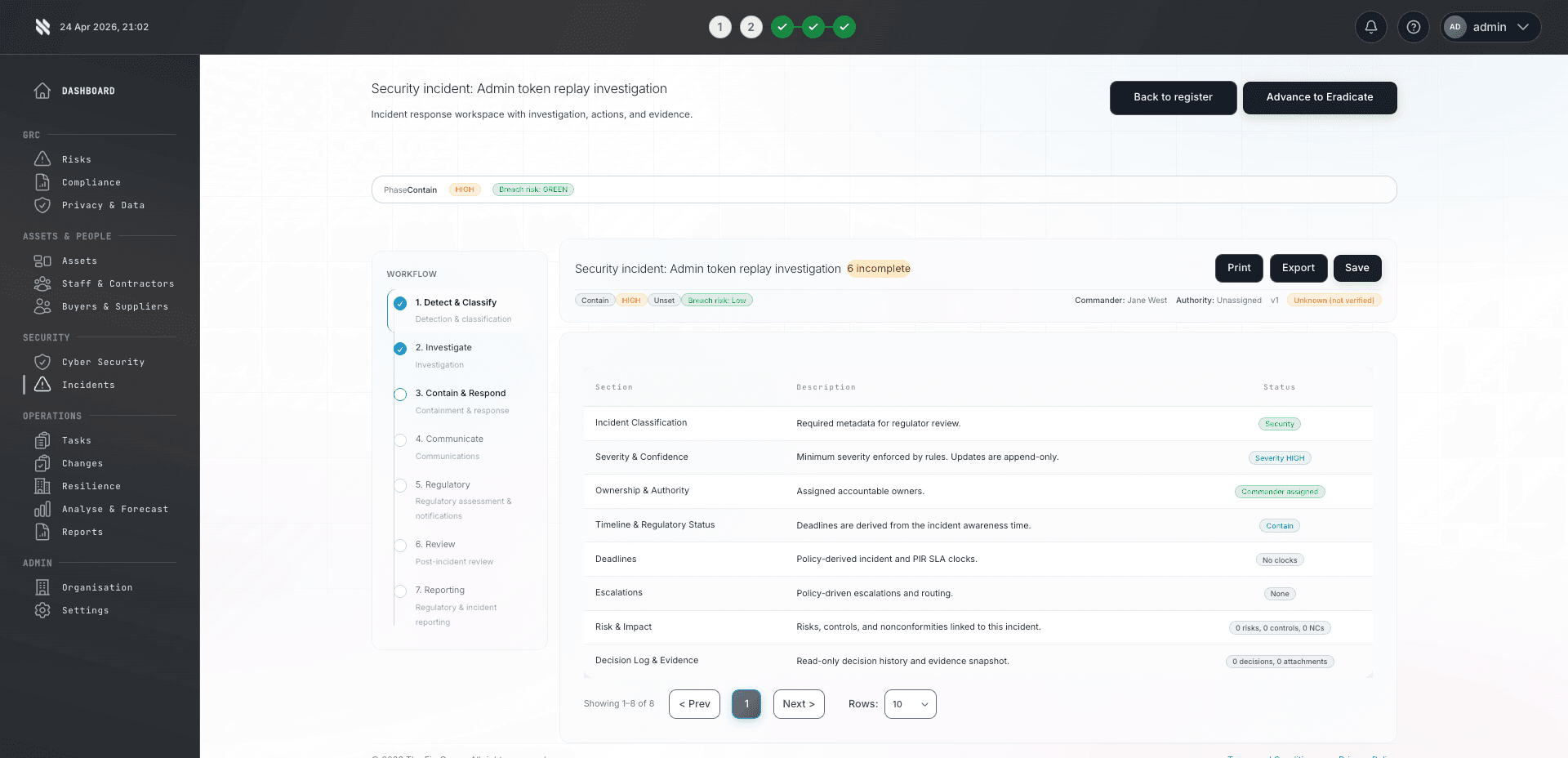
Respond / Incident Management
Run incidents with evidence captured as the work happens.
Manage response actions, owners, decisions, notifications and reporting from one structured incident record.
- Keep response timelines defensible.
- Connect incidents to risks and controls.
- Support client, regulatory and insurance reporting.
Respond / Agentic Remediation
Move from finding to fix without losing control.
Use guided remediation to turn findings into assigned actions while keeping human approval, ownership and evidence intact.
- Suggest next actions from context.
- Assign remediation to owners.
- Verify and evidence completion.
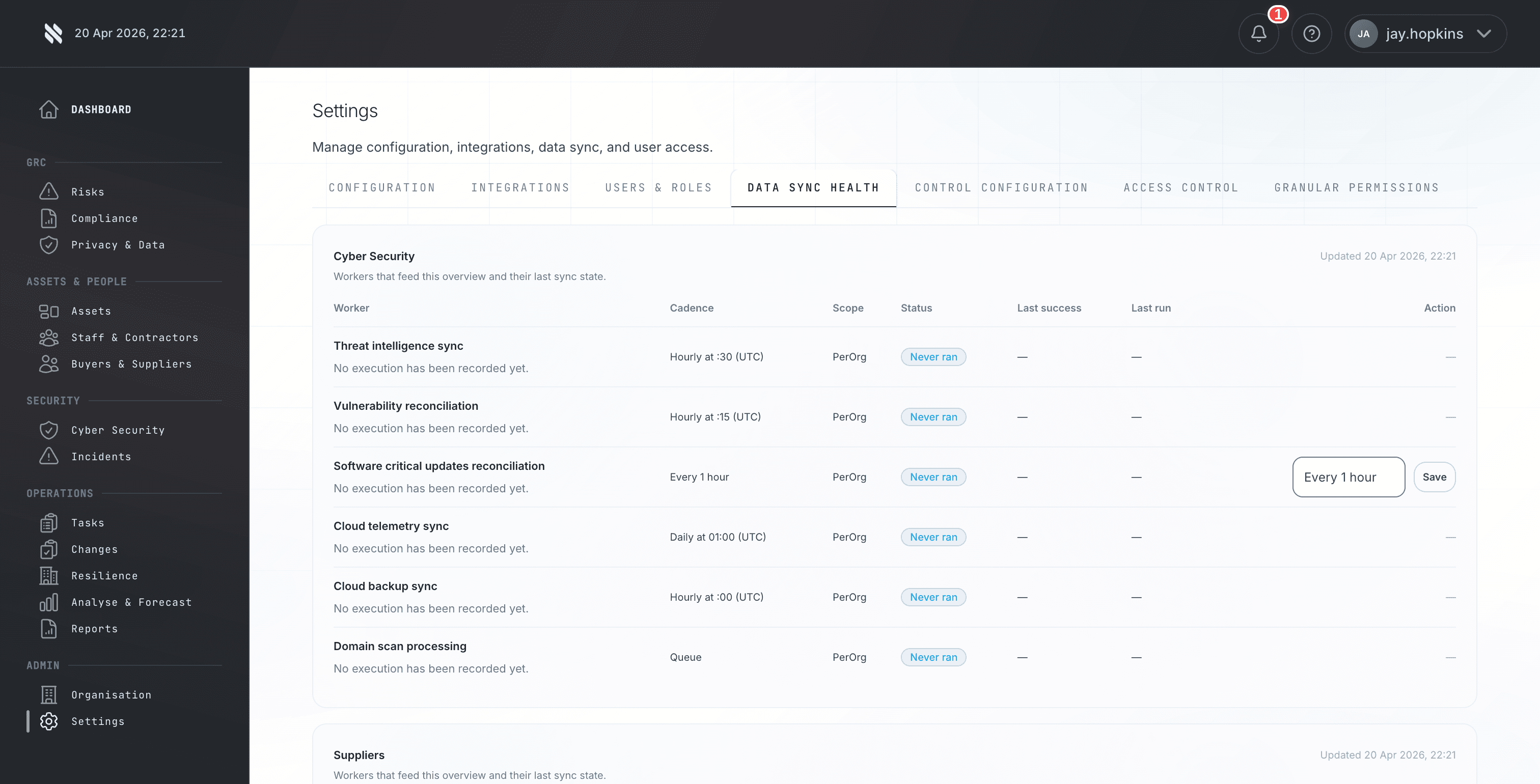
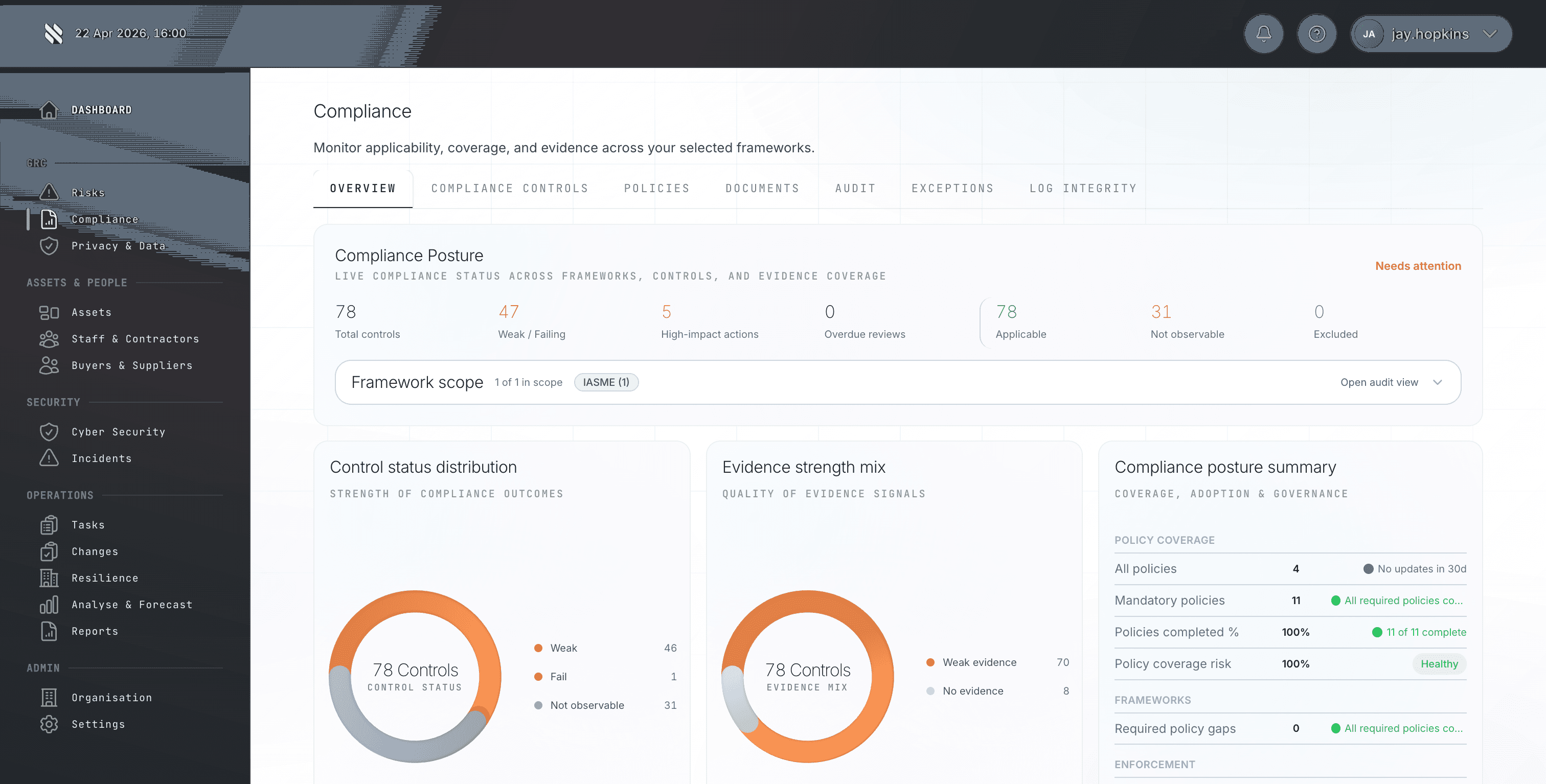
Prove / Compliance Automation
Keep compliance current instead of rebuilding it for every audit.
Map controls to frameworks, collect evidence continuously and expose gaps while there is still time to act.
- Reuse evidence across frameworks.
- Detect stale or missing evidence.
- Generate audit-ready status from live work.
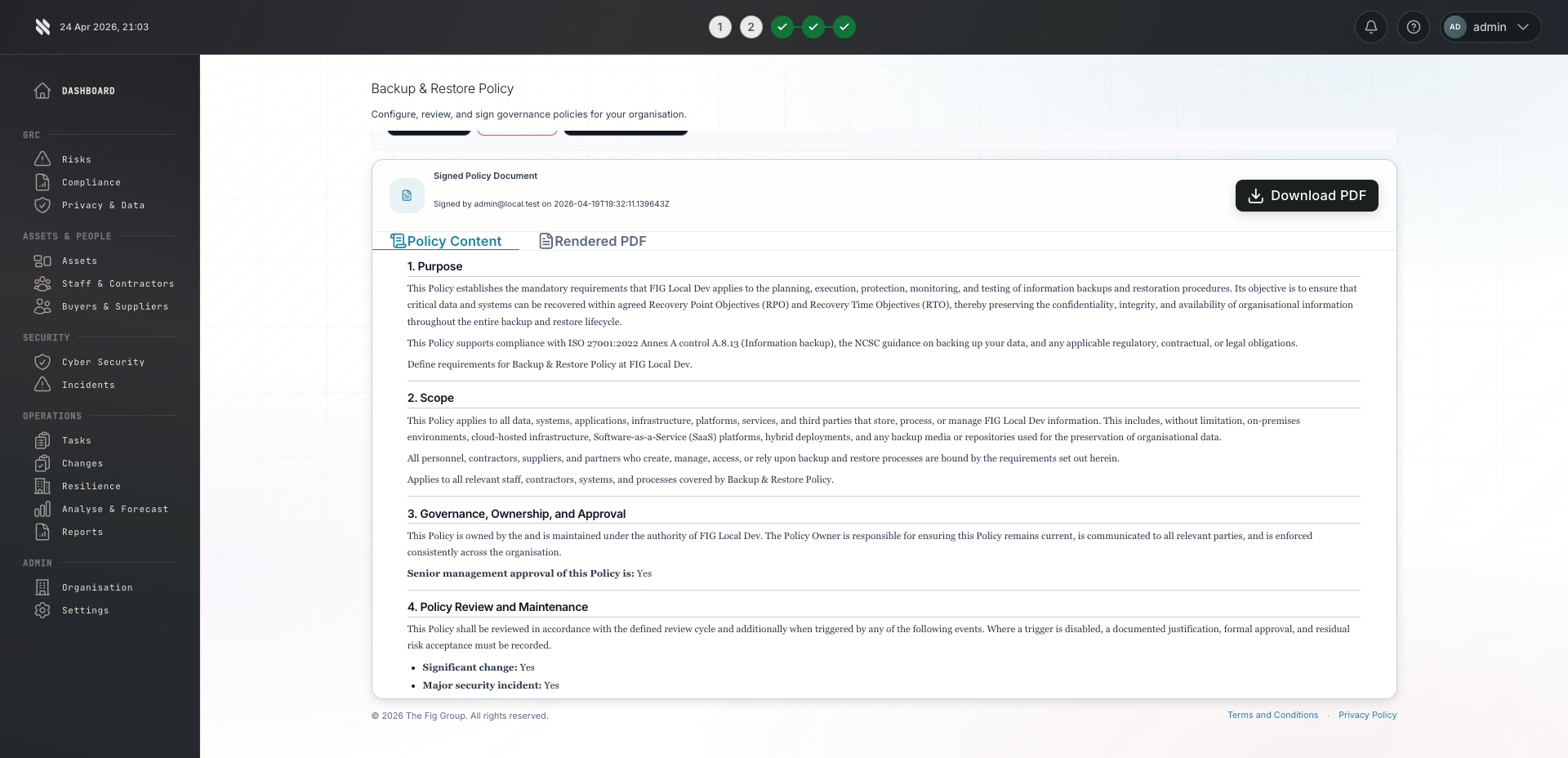
Prove / Policy Management
Turn policies into operational control, not static documents.
Connect policies to owners, approvals, exceptions, attestations and the controls they are supposed to govern.
- Manage reviews and approvals.
- Track staff acknowledgement.
- Link policy obligations to evidence and tasks.
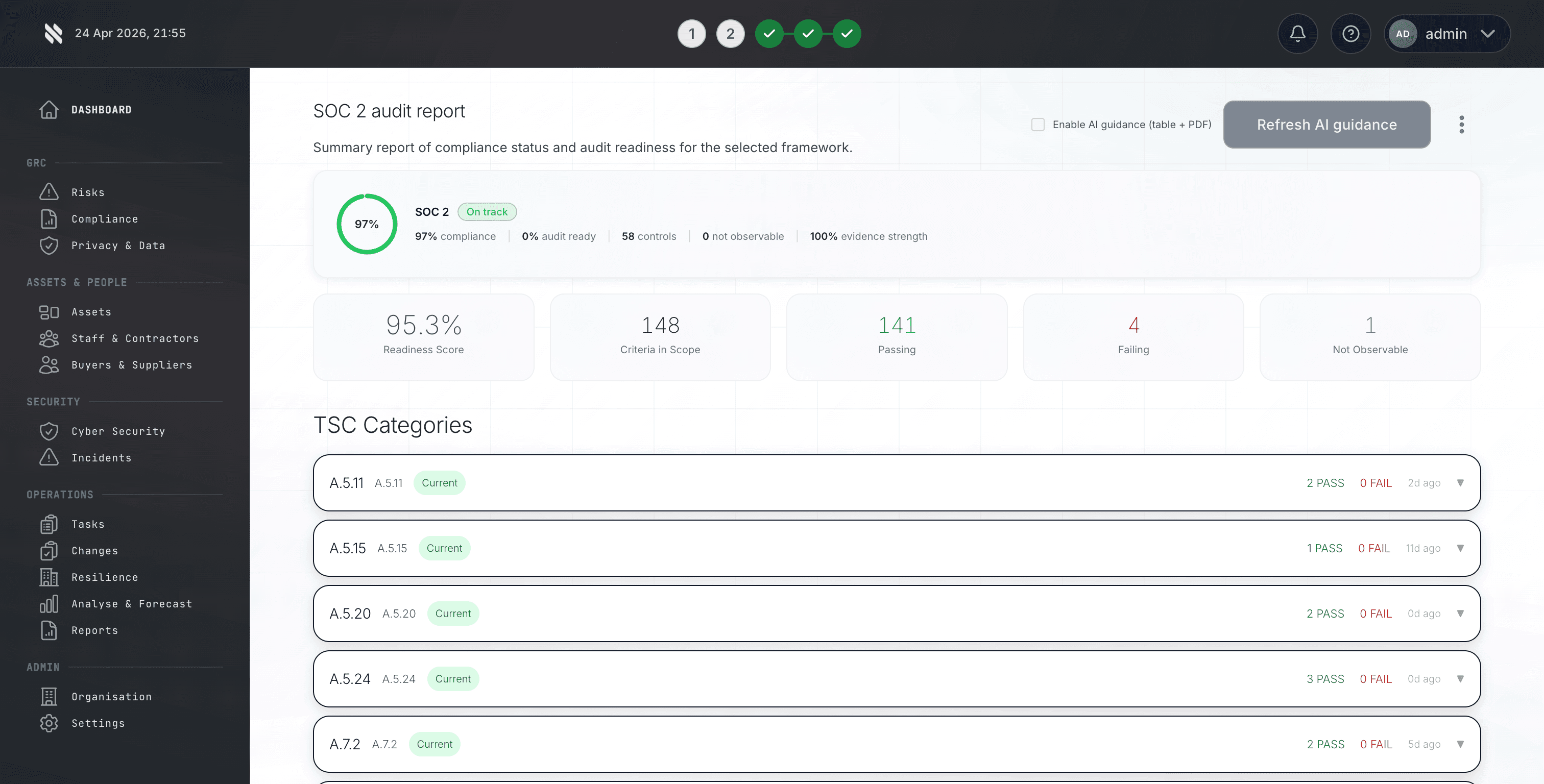
Prove / Audit Management
Build audit packs from work that already happened.
Plan audits, organise evidence, track findings and prove remediation without creating a parallel spreadsheet process.
- Organise evidence by requirement.
- Track findings to closure.
- Give auditors clear ownership and status.
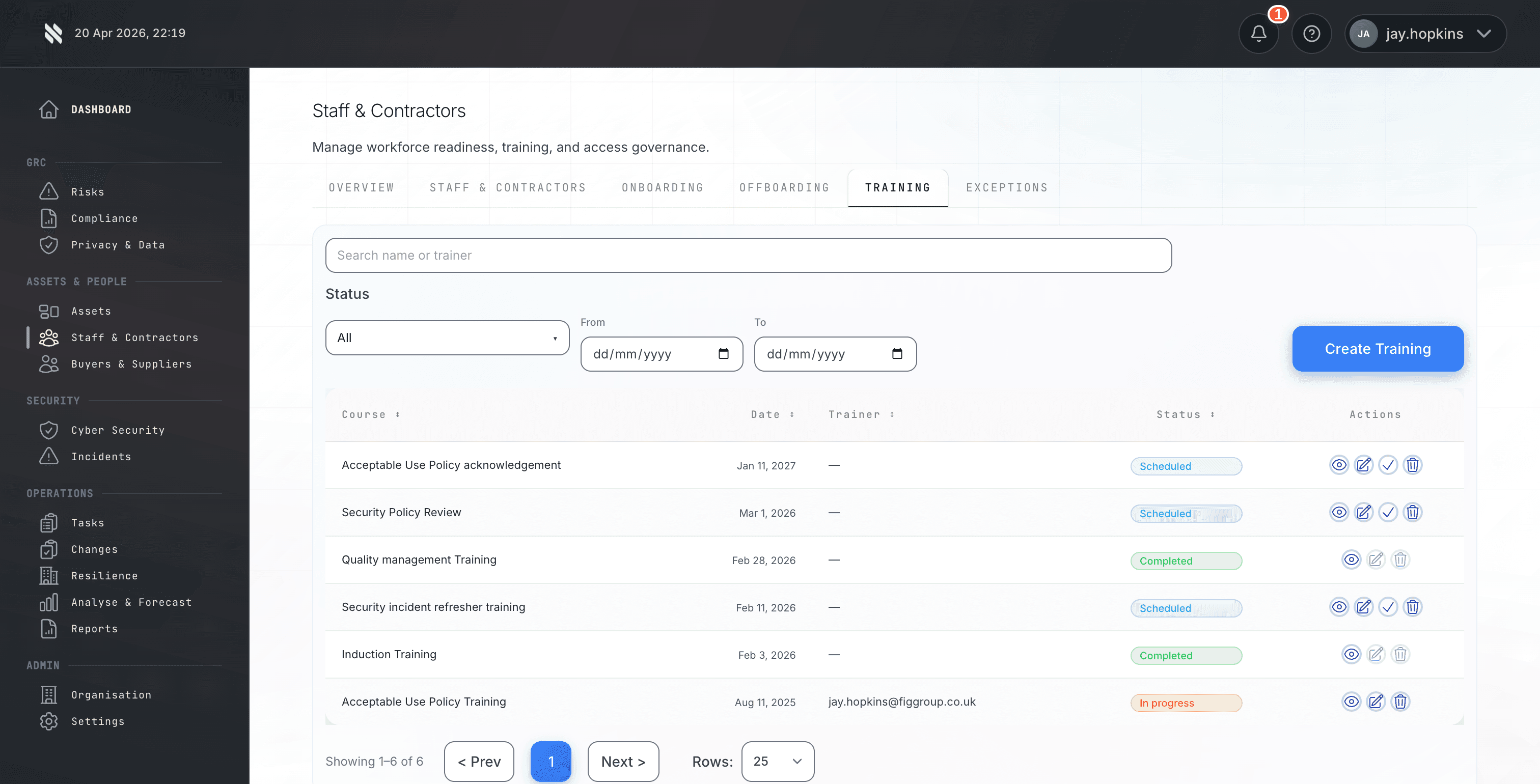
Prove / Training & Policy Acknowledgement
Prove that people have been trained and policies have been acknowledged.
Track training obligations, policy acknowledgements, completion evidence, exceptions and gaps against the frameworks and policies that require them.
- Assign role-based training and policy acknowledgements.
- Evidence completion, exceptions and overdue actions.
- Identify gaps before assessment or audit.
Transfer / Insurance
Use security evidence to support better insurance conversations.
Turn posture, compliance and risk data into a clearer underwriting story for renewals, submissions and client advisory.
- Reuse live risk and control evidence.
- Support cyber insurance readiness.
- Connect remediation to renewal confidence.
Next step
See the platform on your own data.
48-hour deployment. 65+ frameworks. 300+ integrations. Speak to our team or start with the free Cyber Essentials readiness checker.