Compliance tools observe. Fig enforces.
Most compliance platforms sit beside your tools and watch. Fig sits across them and acts - a fully operational IT service management (ITSM) layer that enforces governance based on your selected frameworks and your internal policies. Not the minimum bar, but the actual standards your organisation has committed to.
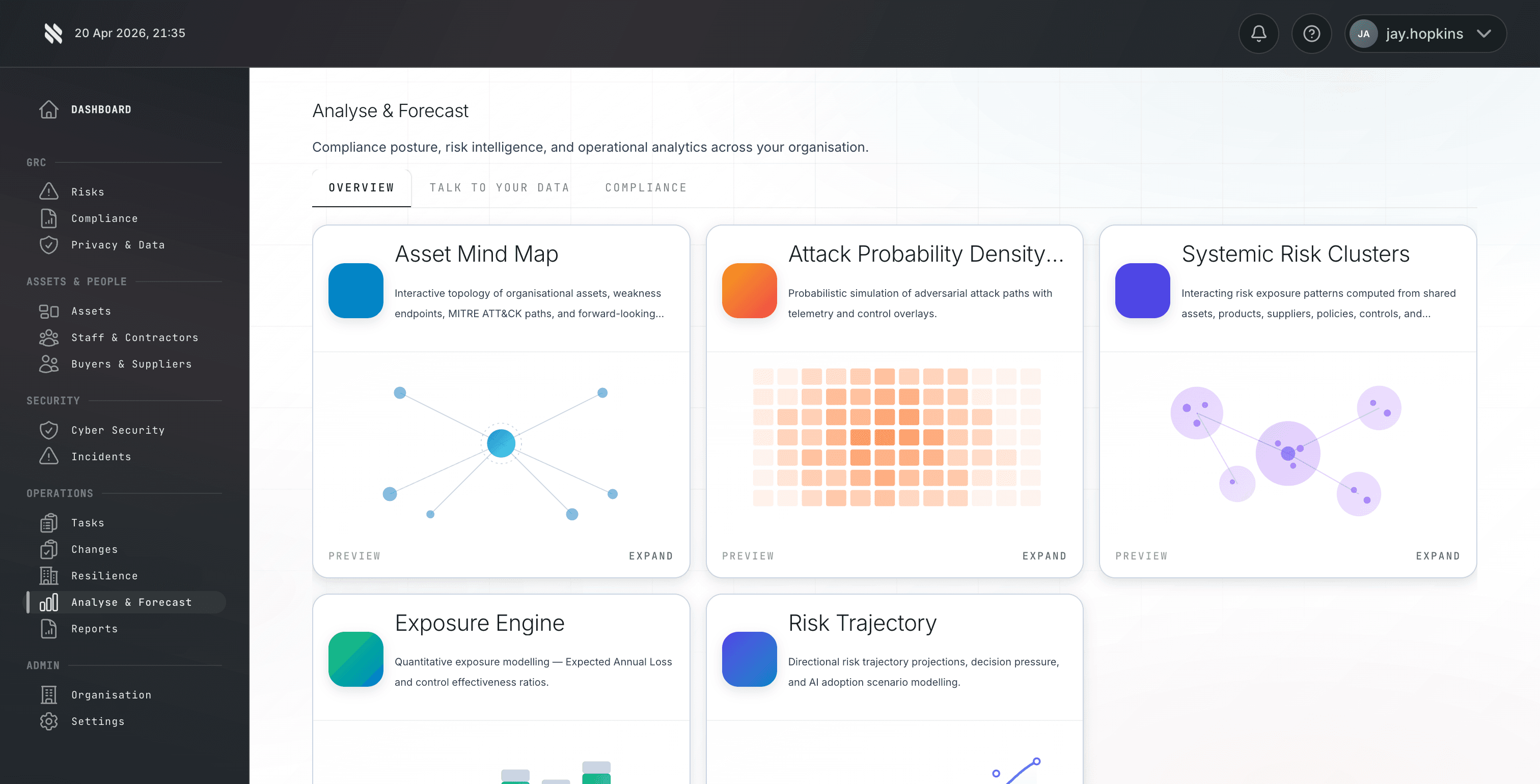
See where attacks are most likely to land.
Fig analyses your environment to map attack probability density, highlighting the entry points and pathways that carry the highest risk.
Compliance automation has a blind spot.
The industry built tools that watch. Fig built a platform that acts.
Signal observers, not operational platforms
Existing tools connect to your stack with read-only access. They observe signals and report on status. But they do not sit in the operational flow. When something drifts, they flag it - they do not prevent it.
Framework minimums, not your actual commitments
Your clients do not care whether you meet the minimum bar for ISO 27001. They care whether you meet the commitments in their due diligence questionnaire (DDQ) - your internal policies that often go well beyond framework requirements.
MSP and corporate misalignment
The corporate sets internal policy standards. The MSP enforces framework minimums using an observation tool. The gap between the two is invisible until a client audit surfaces it - and by then, trust is damaged.
Data lives in silos
Corporate data and MSP data have always lived in separate systems, requiring manual reports to bridge the gap. But these datasets are not independent - they are dependent.
Frameworks and policies in. Enforced governance out.
Fig takes your selected compliance frameworks and your internal policies, connects across your entire tool stack, and turns them into enforceable operational governance.
Select your frameworks. Build your policies.
Start with the compliance frameworks you need - ISO 27001, Cyber Essentials, Defence Cyber Certification (DCC L0/L1) for MOD-supply-chain work, SOC 2, or any other standard. Then layer on your internal policies: the commitments from your DDQs, your board-approved standards, the controls that go beyond the framework minimum.
Fig connects across your entire toolset
Fig integrates with your endpoint management, identity provider, vulnerability scanner, SIEM, cloud platforms, and more. Unlike observation tools, Fig sits in the operational flow. Events get routed, assigned and actioned through the platform.
Frameworks and policies drive the ITSM
Fig is a fully operational ITSM - not a dashboard bolted onto someone else's. Every ticket, workflow, escalation and SLA is governed by both the framework requirements and the corporate's internal policies.
MSP and corporate operate from one platform
Both parties see the same policy-driven requirements. The MSP knows exactly what the corporate expects because it is encoded in the system - not interpreted from a framework document.
Every event tracked from trigger to closure
When something fires in the corporate's integrated stack, Fig triggers a workflow aligned to the relevant policy. Every event has an owner, a policy-driven SLA, and a full audit trail. Compliance is enforced in real time, not checked after the fact.
One digital estate. One view. For the first time.
Corporate data and MSP data have always lived in silos - separate systems, separate reports, separate versions of the truth. Fig connects those datasets.
Data bridged by manual reports
Corporate systems: asset registers, policy documents, risk assessments, board reports, internal audit findings.
MSP systems: endpoint telemetry, vulnerability scans, patching status, incident tickets, remediation logs.
Neither party has the full picture.
One operational platform
Corporate sees: real-time enforcement status, MSP actions against their policies, full evidence chain.
MSP sees: exact policy requirements per corporate, assigned actions, tracked SLAs, closure evidence.
For the first time, both parties have a connected view governed by the corporate's own policies.
Fig vs compliance monitoring tools.
A direct comparison against platforms like Vanta, Drata, and other compliance automation tools.
| Capability | Fig | Others |
|---|---|---|
| What it is | A fully operational IT service management (ITSM) layer that sits across your entire toolset and enforces governance. | A signal observer that monitors tools and reports on compliance status. |
| Compliance approach | Enforces both framework requirements and your internal policies that go beyond them. | Monitors against minimum framework thresholds only. |
| Integration model | Operational layer across your entire GRC stack - events flow through Fig, not past it. | Read-only connectors that observe your tools and surface alerts. |
| Policy management | Corporates build their own policies in the app; these drive all operational governance. | Pre-built templates mapped to framework minimums. |
| MSP-corporate alignment | Both parties governed by the same policy-driven rules in a shared operational platform. | MSPs interpret frameworks independently; corporates hope for the best. |
| Event handling | Events from integrated tools trigger policy-aligned workflows and assigned actions. | Events flagged for manual review against framework checklists. |
| Responsibility tracking | Every task has a clear owner, tracked from event to closure with enforced SLAs. | Shared dashboards with ambiguous ownership. |
| Data model | Corporate and MSP data connected in one platform, providing a single view of the digital estate. | Corporate and MSP data in separate silos, bridged by manual reports. |
| Gap prevention | Policy enforcement means gaps cannot form - the platform will not allow it. | Gaps discovered at audit time, one or more quarters after they appeared. |
"Corporates had their data. MSPs had theirs."
I spent years dealing with client DDQs that outlined what their internal policies actually required. Then I would look at what the MSPs were delivering - minimum framework thresholds from off-the-shelf compliance tools. The two never matched.
Fig exists to connect those datasets for the first time. Not as a reporting layer, but as the operational platform that both parties work through - enforcing the standards your organisation has actually committed to, and making sure everyone responsible can see it, own it, and prove it.
- Jay Hopkins, Founder, The Fig Group
Built for corporates and MSPs.
Fig aligns corporates and their MSPs on a single platform, governed by the corporate's own policies.
Your policies. Enforced. Visible. Proven.
Build your actual policies into the platform
Not framework templates. Your board-approved, DDQ-committed, client-facing standards - structured as enforceable operational rules.
See exactly what your MSP is doing
Every event, every response, every resolution - tracked against your policy requirements, not their interpretation of a framework.
Events trigger your policy, not a generic checklist
When your GRC stack flags something, Fig routes it through your policy logic. The response matches what you committed to, every time.
Audit-ready by default
Full traceability from event to closure. When a client or regulator asks for evidence, it is already there - structured around your policies.
Know what each client needs. Deliver it. Prove it.
No more guesswork on client expectations
Each corporate's policies are in the platform. You see exactly what they require - not what a framework says is the minimum.
Responsibilities are clearly defined
Who owns what is encoded in the system. When an event occurs, the right party is notified with the right action.
Demonstrate value with evidence, not reports
Every action you take is tracked against the corporate's policy. You are not writing quarterly reports - the evidence builds itself.
Scale without dropping standards
Each client's policies are enforced independently. Growing your book does not mean diluting your service.
One platform. Eight tools replaced.
Fig is not another tool to add to your stack. It replaces standalone products you are already paying for.
OneTrust
Privacy management
ServiceNow Change
Change governance
HackerOne
Vulnerability disclosure
PagerDuty
Incident workflows
MasterControl
Quality management
PowerDMS
Policy management
KnowBe4
Training and awareness
Broker portals
Insurance placement
Common questions.
How Fig compares to other compliance platforms.
How is Fig different from Vanta or Drata?
Vanta and Drata focus on SOC 2 and ISO 27001 monitoring. They connect to your tools with read-only access and report on compliance status. Fig is an operational platform that enforces governance - events flow through Fig, get matched to your policies, trigger assigned actions, and are tracked to closure. Fig also includes embedded insurance, which no other compliance platform offers.
Is Fig a replacement for our existing security tools?
No. Fig sits across your existing tools as an operational governance layer. Your SIEM, EDR, identity provider, and cloud platforms stay in place. Fig connects to them, routes events through policy-driven workflows, and ensures every action has an owner and an audit trail.
How does Fig handle the MSP-corporate relationship?
Both parties operate from the same platform with the same policy-driven rules. The corporate builds their policies in Fig. The MSP sees exactly what is expected and acts on it. Responsibilities are defined, SLAs are enforced, and both sides see the same compliance data in real time.
What happens when a compliance gap appears?
Fig does not just flag gaps - it prevents them. Because governance policies are enforced operationally, deviations trigger workflows immediately rather than being discovered at audit time. When remediation is needed, Fig creates the task, assigns the owner, sets the SLA, and tracks it to closure.
How quickly can we deploy Fig?
Most organisations are live within 48 hours. Setup involves selecting your frameworks, configuring your policies, and connecting your existing tools via 300+ integrations. No migration, no disruption.
Does Fig work for organisations that do not use an MSP?
Yes. Corporate risk teams use Fig independently for internal compliance management, policy enforcement, and audit readiness.
Ready to see the difference?
See how Fig turns your internal policies into operational governance that keeps corporates and MSPs aligned at all times.