Lifecycle
Where it sits in the operating model
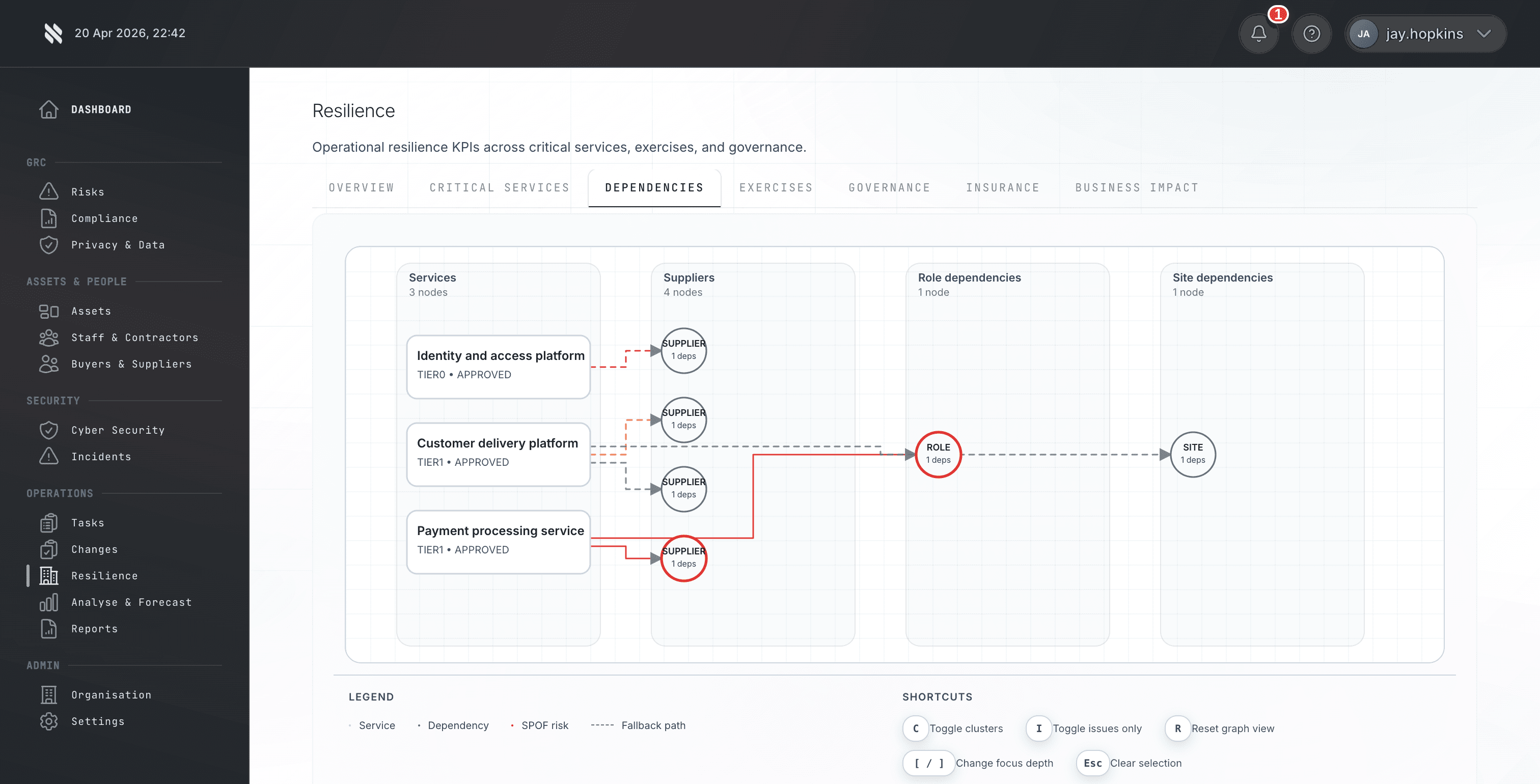
The Protect phase is where this capability sits in the wider Fig operating model. Third-party vendor risk is assessed once per contract, then forgotten. Supplier compliance drifts. Breaches at critical partners go undetected until they impact you. Fig turns that problem into a repeatable lifecycle so MSPs, risk teams, and auditors are not relying on static spreadsheets or ad hoc screenshots when a buyer asks for proof.