Lifecycle
Where it sits in the operating model
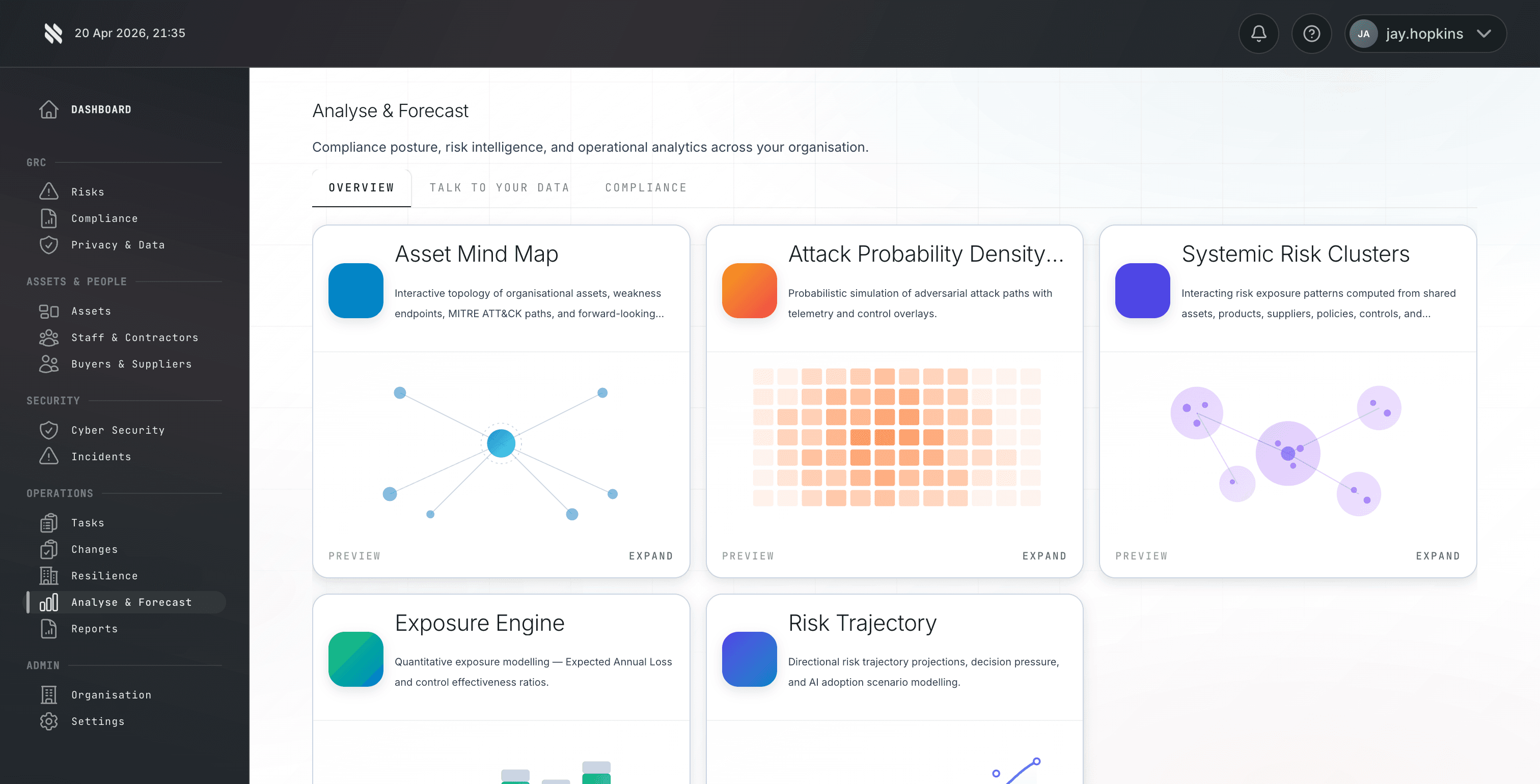
The Protect phase is where this capability sits in the wider Fig operating model. Individual risk scores don't show aggregate exposure. You don't know whether one more vulnerability tips you into breach-likely territory. Scenario planning is impossible. Fig turns that problem into a repeatable lifecycle so MSPs, risk teams, and auditors are not relying on static spreadsheets or ad hoc screenshots when a buyer asks for proof.