Lifecycle
Where it sits in the operating model
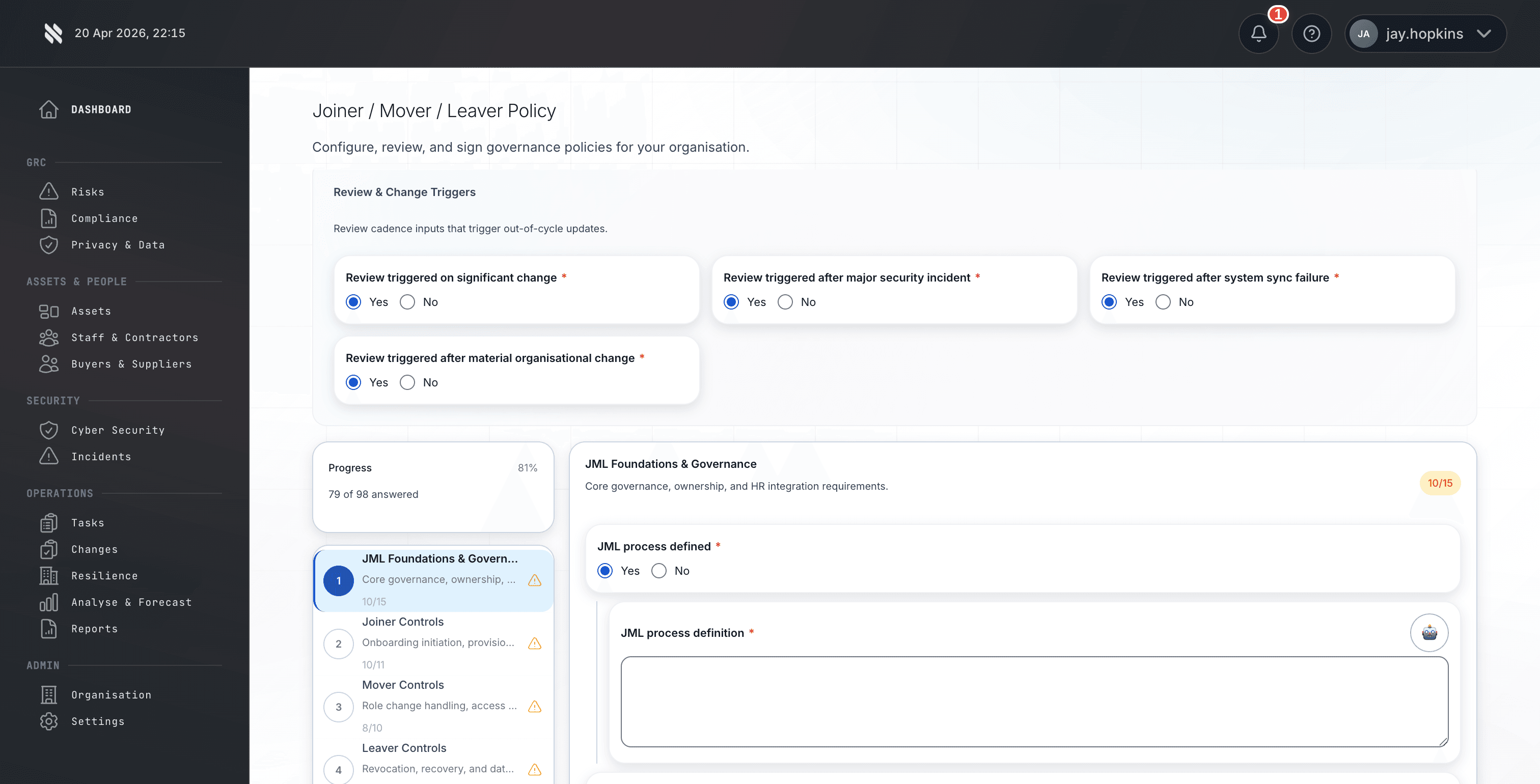
The Prove phase is where this capability sits in the wider Fig operating model. Policies age without review. Staff never see them. Attestation is manual and incomplete. Policy drift goes undetected. Compliance officers spend weeks on administrative work instead of governance. Fig turns that problem into a repeatable lifecycle so MSPs, risk teams, and auditors are not relying on static spreadsheets or ad hoc screenshots when a buyer asks for proof.