Lifecycle
Where it sits in the operating model
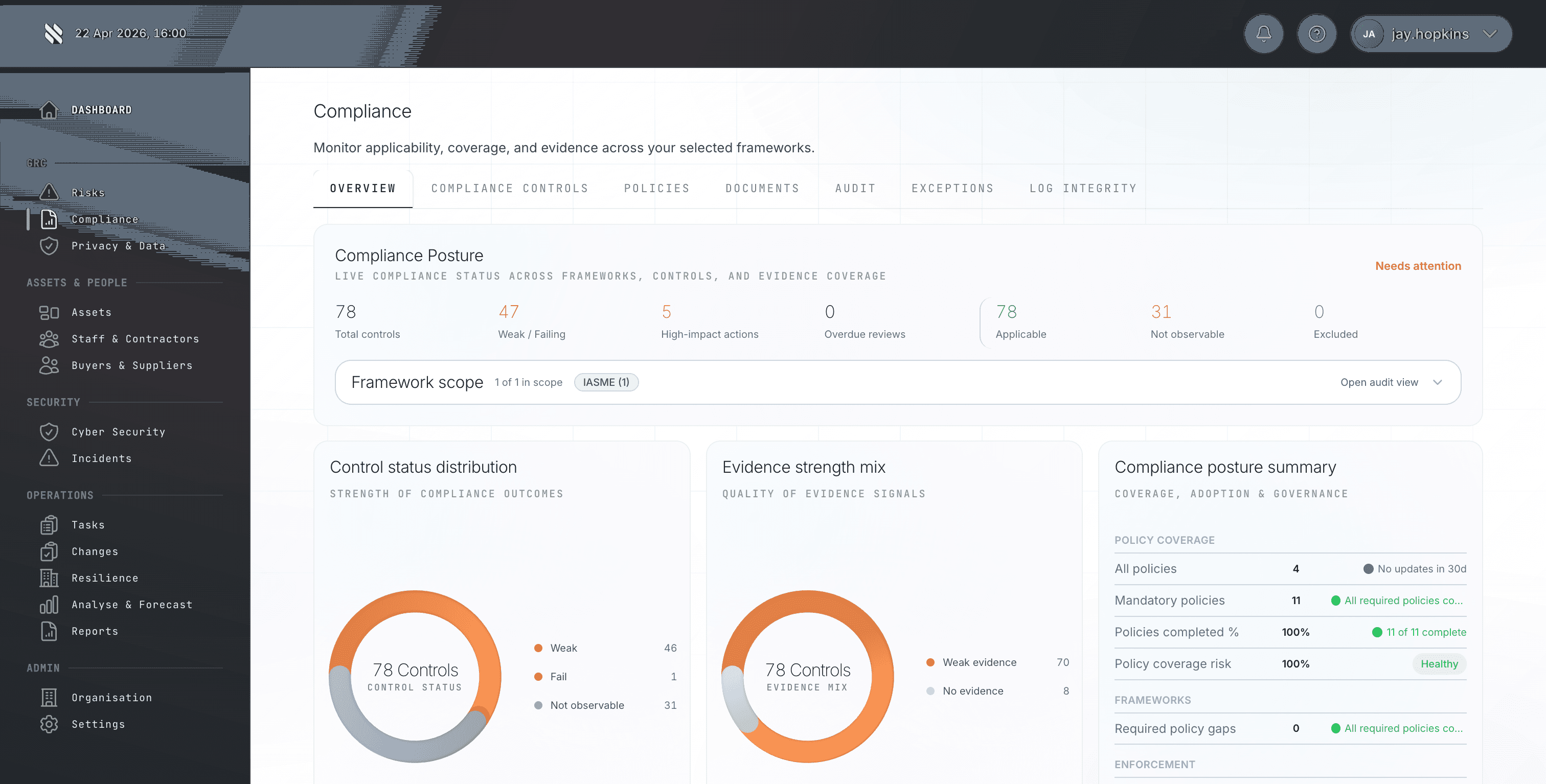
The Prove phase is where this capability sits in the wider Fig operating model. Compliance evidence is assembled once per audit. Framework mapping is inconsistent. New regulations hit without warning. Manual control assessment breaks teams under scale. Fig turns that problem into a repeatable lifecycle so MSPs, risk teams, and auditors are not relying on static spreadsheets or ad hoc screenshots when a buyer asks for proof.